Card Application Solutions
End-to-end business mapping with practical device selection and implementation recommendations.
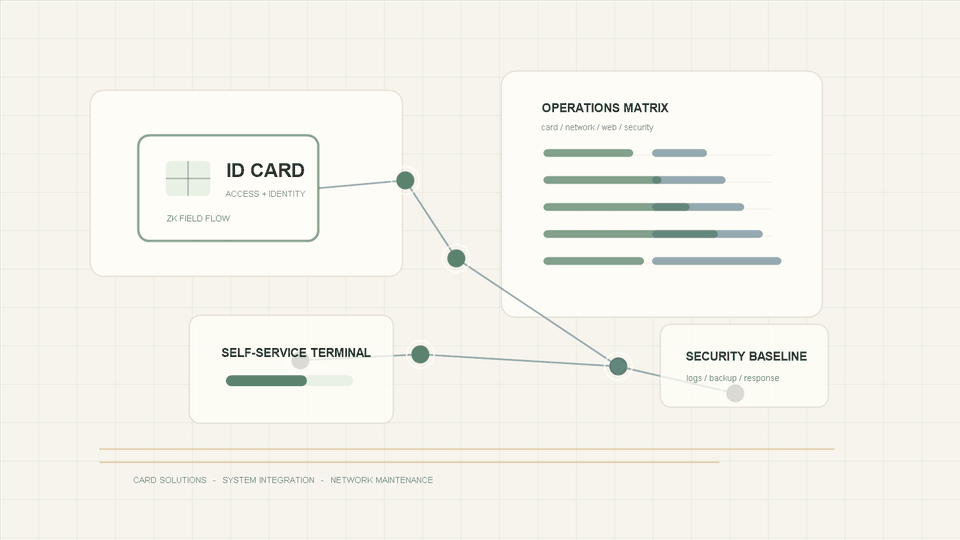
ZhengKa supports card applications, self-service terminals, network environments, websites, and security maintenance with practical consulting from solution design and hardware-software integration to long-term operations, improving delivery efficiency and operational stability in complex field environments.
CPU
--%
Memory
--%
Uptime
--
Visitor IP
0.0.0.0
OS
--
Browser
--
End-to-end business mapping with practical device selection and implementation recommendations.
Connect card readers, self-service terminals, business systems, databases, and third-party interfaces to reduce long-term maintenance friction.
Design network topology, VPN, remote access, link redundancy, and troubleshooting paths for stores, campuses, server rooms, and branches.
Build corporate websites, downloads, contact forms, and basic admin panels into business-grade portals with SEO and interaction capabilities.
Establish a security baseline across accounts, data, servers, websites, and remote access, including log auditing, disaster recovery backups, and incident response.
Provide staged reviews, field support, vendor coordination, and continuous improvement for teams without a complete in-house technical function.
Card issuance, access control, payment, self-service, and permission management working together.
Card readers, terminal programs, backend APIs, and databases operating as one flow.
Stores, branches, server rooms, VPNs, and remote support links designed for continuity.
Websites, authorized downloads, contact forms, SEO, and basic admin controls in one place.
Clarify business workflows, equipment conditions, network boundaries, user permissions, and maintenance capacity before designing the solution.
Define system structure, device lists, interface boundaries, deployment paths, and risks so cost and maintenance impact are visible early.
Complete deployment, integration testing, permission setup, backup strategy, and handover in stages to reduce post-launch uncertainty.
Update configuration, patches, security policies, and monitoring indicators as the business changes.
We focus on whether the site can be maintained over time: who operates it, where it can fail, how to troubleshoot remotely, how data is backed up, how permissions are controlled, and how devices are replaced.
Critical steps have backups, fallback paths, and clear responsibilities.
Inputs and outputs between software, hardware, databases, and third-party platforms are traceable.
Remote support, logs, handover documents, and permission policies are delivered together.
Account, network, server, and website security are designed from the start rather than patched later.
Start with a consultation, a small website, a network issue, or a card-application improvement project.